TOTPRadius VPN Portal - Overview
While classic OTP (and namely TOTP) still remains industry standard for two-factor authentication and is supported out of the box by the majority of VPN clients, there is not a lot of products that can leverage the FIDO keys for securing VPN access. The majority of the current solutions that are being marketed as supporting FIDO and FIDO2 keys are using the OTP functionality of the security keys (most USB FIDO keys, in addition to U2F and/or WebAuthn features, also have an additional module that can generate OTP, i.e. HOTP by pressing a button, or TOTP via a companion app). This may look like a solution but is still an OTP-based approach. While OTP solutions are still secure, utilizing FIDO keys' main features to protect VPN access may improve security even further. In addition to FIDO security keys, using single sign on features of Azure AD (Microsoft Entra ID) is also something that we see as a critical feature to offer.To address these gaps, TOKEN2 has introduced an additional feature, called VPN Portal, as a part of its TOTPRadius solution, to provide VPN access beyond in the classic TOTP authentication: FIDO Security keys and Azure AD (Microsoft Entra ID) OAuth2 based Single Sign On (SSO) .
The FIDO VPN Portal solution will work with both FIDO2 and FIDO keys (WebAuthn implementation with fallback to U2F for older keys), with a possibility to enable Passwordless method (FIDO2 only) and will work via modern web-browsers supporting FIDO keys authentication.
The OAuth2 Portal will leverage Azure AD (Microsoft Entra ID) OAuth2 SSO option and will allow extending the login procedures the users are already familiar with, to the VPN connectivity procedures. If users have previously logged on to any M365 resource using the same Azure AD (Microsoft Entra ID) Account, the OAuth2 login will be automatic and will not ask to re-login again to use the VPN Portal.
VPN Portal Network configuration
If you wish to implement FIDO2/Passwordless or Azure AD (Microsoft Entra ID) Oauth2/SSO VPN access for your users (available starting from v0.2.5), there is an additional configuration required in your network layout. The web portal is running as a separate web server on the same virtual appliance, instead of standard https port (443) used for admin interface, the VPN web portal responds on port 9443. This port cannot be used directly for technical reasons, so has to be NATted to port 443. More information about this network layout is available here.
VPN Portal security
 For obvious reasons, this portal has to be exposed to the public network. We understand the potential risks of making a web application accessible to the whole planet, therefore to ensure the security of the VPN Portal is at the highest level, we have contracted an independent security institution to conduct a full penetration testing against this web application and produce a report. The outcomes of this test are available here.
For obvious reasons, this portal has to be exposed to the public network. We understand the potential risks of making a web application accessible to the whole planet, therefore to ensure the security of the VPN Portal is at the highest level, we have contracted an independent security institution to conduct a full penetration testing against this web application and produce a report. The outcomes of this test are available here.
- Classic 2FA or Passwodless login
- FIDO2 and FIDO (U2F) hardware support
- Self-enrollment using LDAP or local passwords
- read more...
- Simple configuration in Azure AD (Microsoft Entra ID)
- Seamless user login experience (SSO)
- Azure AD (Microsoft Entra ID) controlled access restrictions
- read more...
About
Installation and configuration
- Installation and initial configuration
- Network configuration
- Migrating from older versions
- LDAP Configuration
- Azure AD Configuration
- Self-service enrollment portal
- Web and LDAPS Certificates
- Syslog configuration
- Single-factor authentication exceptions
- Slave appliance mode
- Dynamic RADIUS Attributes
Integration guides
Blog
04-04-2026
Understanding FIDO User Verification Modes and the always_uv Setting
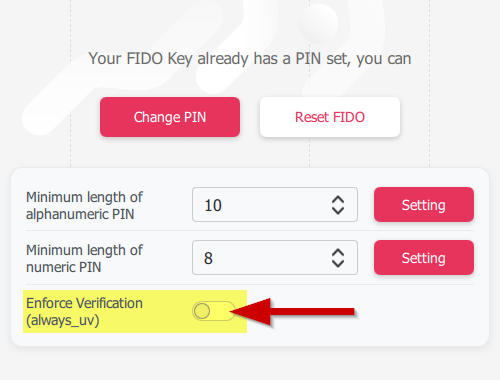 Token2 R3.3 and later FIDO2 keys enforce user verification by default with always_uv = true, improving security, though some platforms and apps like Windows 10, macOS, and certain legacy clients may fail to handle this override correctly.
Token2 R3.3 and later FIDO2 keys enforce user verification by default with always_uv = true, improving security, though some platforms and apps like Windows 10, macOS, and certain legacy clients may fail to handle this override correctly.
05-03-2026
Introducing TOTPVault — self-hosted TOTP management for teams
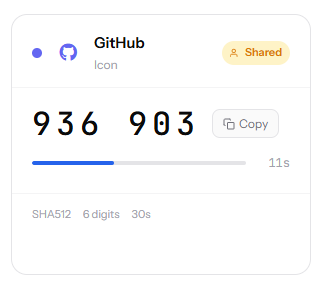 Most TOTP apps work by distributing copies of the secret to every person who needs access — fine for personal accounts, but for shared service accounts it means MFA secrets scattered across people's phones with no clean way to revoke access when someone leaves.
Most TOTP apps work by distributing copies of the secret to every person who needs access — fine for personal accounts, but for shared service accounts it means MFA secrets scattered across people's phones with no clean way to revoke access when someone leaves.
21-12-2025
Android, NFC, and the Missing Piece of WebAuthn
 For years, Android users have faced a frustrating limitation—Android does not support CTAP2 over NFC. This means no PIN verification and no discoverable credentials (passkeys) when using NFC, and therefore limited to simple U2F-style flows without user verification. That said, there finally seems to be a solution.
For years, Android users have faced a frustrating limitation—Android does not support CTAP2 over NFC. This means no PIN verification and no discoverable credentials (passkeys) when using NFC, and therefore limited to simple U2F-style flows without user verification. That said, there finally seems to be a solution.
