04-04-2026
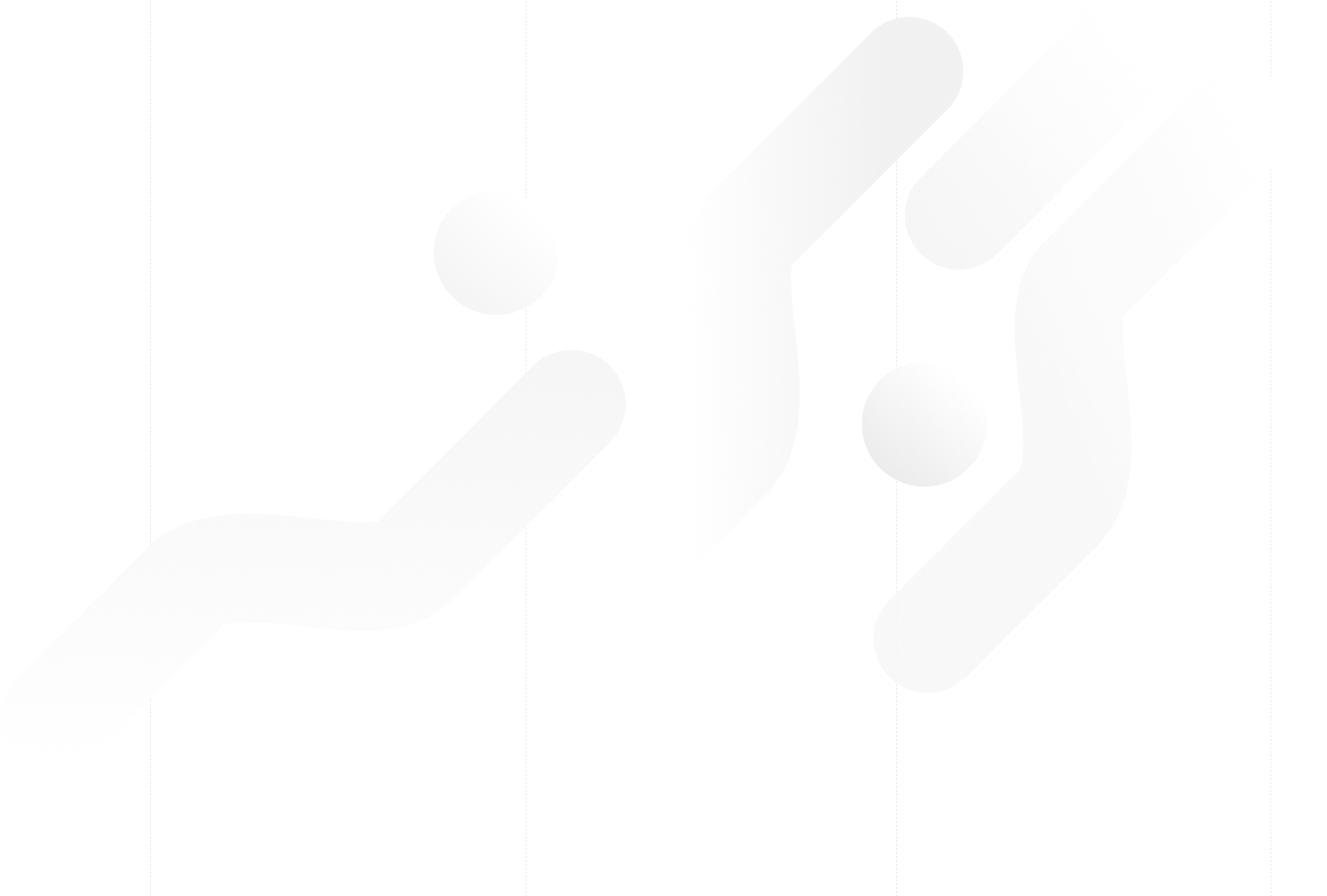
Understanding FIDO User Verification Modes and the always_uv Setting
 Token2 R3.3 and later FIDO2 keys enforce user verification by default with always_uv = true, improving security, though some platforms and apps like Windows 10, macOS, and certain legacy clients may fail to handle this override correctly.
Token2 R3.3 and later FIDO2 keys enforce user verification by default with always_uv = true, improving security, though some platforms and apps like Windows 10, macOS, and certain legacy clients may fail to handle this override correctly.
guides
05-03-2026
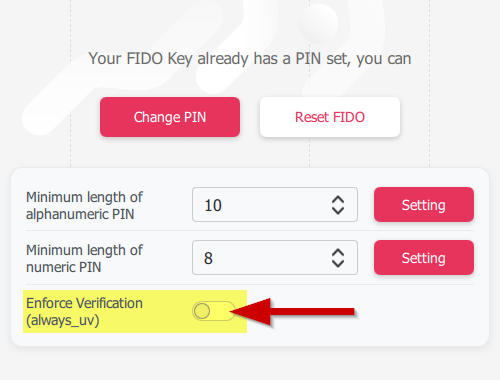
Introducing TOTPVault — self-hosted TOTP management for teams
 Most TOTP apps work by distributing copies of the secret to every person who needs access — fine for personal accounts, but for shared service accounts it means MFA secrets scattered across people's phones with no clean way to revoke access when someone leaves.
Most TOTP apps work by distributing copies of the secret to every person who needs access — fine for personal accounts, but for shared service accounts it means MFA secrets scattered across people's phones with no clean way to revoke access when someone leaves.
tools
21-12-2025
Android, NFC, and the Missing Piece of WebAuthn
 For years, Android users have faced a frustrating limitation—Android does not support CTAP2 over NFC. This means no PIN verification and no discoverable credentials (passkeys) when using NFC, and therefore limited to simple U2F-style flows without user verification. That said, there finally seems to be a solution.
For years, Android users have faced a frustrating limitation—Android does not support CTAP2 over NFC. This means no PIN verification and no discoverable credentials (passkeys) when using NFC, and therefore limited to simple U2F-style flows without user verification. That said, there finally seems to be a solution.
news
19-12-2025
Streamline Token2 Classic Tokens in Okta
 Token2 classic hardware tokens provide phishing-resistant multi-factor authentication for your Okta environment. Our updated integration guide shows you how to deploy them using Okta's Custom OTP authenticator method.
Token2 classic hardware tokens provide phishing-resistant multi-factor authentication for your Okta environment. Our updated integration guide shows you how to deploy them using Okta's Custom OTP authenticator method.
guides
09-12-2025
Framework ExpansionCard Enclosure for Token2 Keys
 Framework laptops are all about modularity. The Framework ExpansionCard 3D-printable enclosure for Token2 PIN+ Type-C keys brings FIDO2 security directly into your device.
Framework laptops are all about modularity. The Framework ExpansionCard 3D-printable enclosure for Token2 PIN+ Type-C keys brings FIDO2 security directly into your device.
updates
16-09-2025
Token2 PIN+ Keys Now Supported by MojeID at High Assurance Level
 MojeID, the Czech national digital identity service operated by CZ.NIC, has officially added Token2 PIN+ security keys to its list of devices accepted for the high assurance (úroveň záruky vysoká) level.
MojeID, the Czech national digital identity service operated by CZ.NIC, has officially added Token2 PIN+ security keys to its list of devices accepted for the high assurance (úroveň záruky vysoká) level.
updates
18-07-2025
Windows 11 Update KB5062553 Breaks FIDO2 Security Key Management
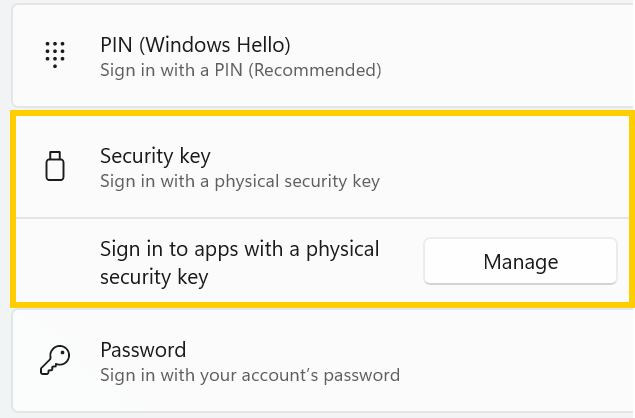 A recent Windows 11 update — KB5062553 — appears to have introduced a critical issue affecting FIDO2 security key management. Update as of 12 September 2025 – This issue is resolved in Windows 11 24H2 (build 26100.6584, KB5065426).
A recent Windows 11 update — KB5062553 — appears to have introduced a critical issue affecting FIDO2 security key management. Update as of 12 September 2025 – This issue is resolved in Windows 11 24H2 (build 26100.6584, KB5065426).
updates
27-06-2025
Token2 PIN+ Bio3 Now Available
 Now Available: Token2 Bio3 – The First Biometric FIDO2 Key with Dual USB-A/USB-C Interface and iOS Fingerprint Management
Now Available: Token2 Bio3 – The First Biometric FIDO2 Key with Dual USB-A/USB-C Interface and iOS Fingerprint Management
new product
06-06-2025
Token2 PIN+ Now Compatible with ID-Austria
 Only a handful of countries have adopted FIDO2 for secure authentication in public services. Switzerland’s AGOV platform was one of the early adopters, and it officially supports Token2 FIDO2 keys. We’re pleased to announce that Austria is now following suit.
Only a handful of countries have adopted FIDO2 for secure authentication in public services. Switzerland’s AGOV platform was one of the early adopters, and it officially supports Token2 FIDO2 keys. We’re pleased to announce that Austria is now following suit.
updates
07-05-2025
FIDO Alliance Passkey Pledge
 Token2 has signed the FIDO Alliance Passkey Pledge - a commitment to supporting and promoting passkeys for simpler, stronger sign-ins.
Token2 has signed the FIDO Alliance Passkey Pledge - a commitment to supporting and promoting passkeys for simpler, stronger sign-ins.
updates
03-03-2025
Understanding Entra’s New Time Drift Allowance
 Microsoft Entra has recently updated its time drift allowances for TOTP, reducing the window to approximately 2 minutes. This change may impact users of hardware tokens that have not been used for an extended period.
Microsoft Entra has recently updated its time drift allowances for TOTP, reducing the window to approximately 2 minutes. This change may impact users of hardware tokens that have not been used for an extended period.
updates
29-01-2025
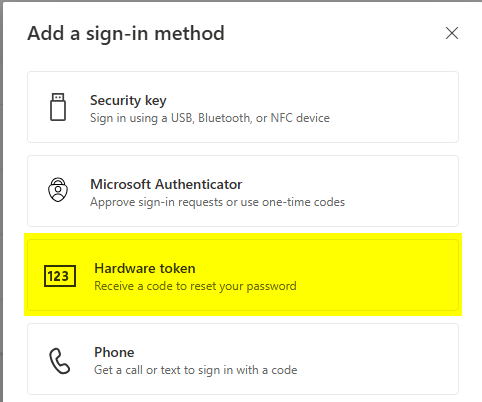
Beware of the Passkey Dialog: Not All Options Are FIDO2 Security Keys
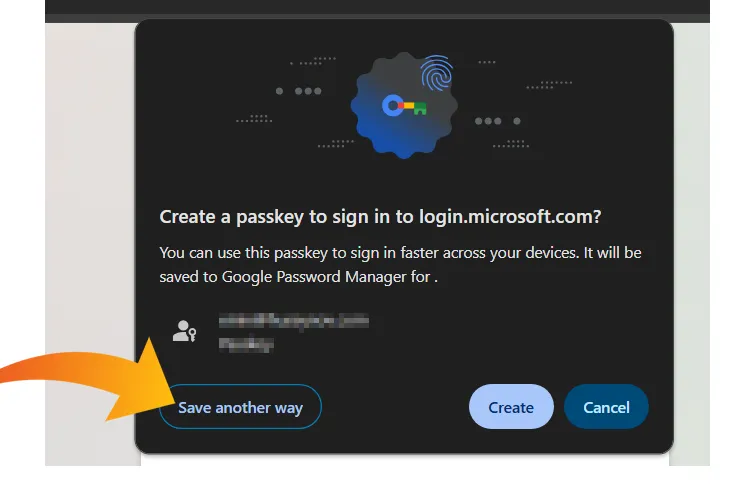 When setting up a passkey on Windows, the standard authentication dialog often presents multiple options for storing credentials.
When setting up a passkey on Windows, the standard authentication dialog often presents multiple options for storing credentials.
guides
09-01-2025
PIN+ Key Series Achieves FIDO Level 2 Certification
 We are thrilled to announce that our PIN+ Key Series has officially obtained FIDO Level 2 (L2) Certification, a significant milestone that underscores our commitment to delivering the highest level of security for our users.
We are thrilled to announce that our PIN+ Key Series has officially obtained FIDO Level 2 (L2) Certification, a significant milestone that underscores our commitment to delivering the highest level of security for our users.
product updates
03-12-2024
Automated FIDO2 Registration for Entra ID
 At Token2, we work to provide organizations with easy-to-use tools. We're excited to share our new manual on FIDO2 Key Automated Registration for Entra ID.
At Token2, we work to provide organizations with easy-to-use tools. We're excited to share our new manual on FIDO2 Key Automated Registration for Entra ID.
tools
25-11-2024
Shipping to Ukraine: Our New Partnership with Nova Post
 After encountering issues with other carriers, we partnered with Nova Poshta for deliveries to Ukraine. Successful test shipments now allow us to proudly offer faster, more reliable delivery with better tracking and service for our Ukrainian customers.
After encountering issues with other carriers, we partnered with Nova Poshta for deliveries to Ukraine. Successful test shipments now allow us to proudly offer faster, more reliable delivery with better tracking and service for our Ukrainian customers.
shipping
22-11-2024
Self-Service for Hardware OATH Tokens in Entra ID with SHA256 Support
 A recent update to Microsoft Entra ID now allows end-users to self-service hardware OATH tokens, removing the need for administrators to manually activate them. Admins can upload hardware tokens into a "public repository" via Graph API, allowing users to assign tokens to their accounts independently.
A recent update to Microsoft Entra ID now allows end-users to self-service hardware OATH tokens, removing the need for administrators to manually activate them. Admins can upload hardware tokens into a "public repository" via Graph API, allowing users to assign tokens to their accounts independently.
updates entra id azure ad
21-11-2024
New iOS 18.1 Update Breaks Support for FIDO2.1 Final Keys
 The latest iOS 18.1 release has introduced an unexpected issue affecting FIDO2.1 Final keys, rendering them incompatible with the new update. This issue is not limited to Token2's security keys but impacts devices from all manufacturers adhering to the FIDO2.1 final specification.
The latest iOS 18.1 release has introduced an unexpected issue affecting FIDO2.1 Final keys, rendering them incompatible with the new update. This issue is not limited to Token2's security keys but impacts devices from all manufacturers adhering to the FIDO2.1 final specification.
updates
10-09-2024
Independent Public Security Review of Token2 PIN+ FIDO2 Security Keys

updates
04-09-2024
Update on EUCLEAK Vulnerability and Chip Security
 We want to assure you that we do not use Infineon chips, which are affected by the EUCLEAK side-channel attack recently identified by NinjaLabs. This attack exploits a vulnerability related to the extended Euclidean algorithm (EEA) used in modular inversion.
We want to assure you that we do not use Infineon chips, which are affected by the EUCLEAK side-channel attack recently identified by NinjaLabs. This attack exploits a vulnerability related to the extended Euclidean algorithm (EEA) used in modular inversion.
updates
Subscribe to our mailing list
Want to keep up-to-date with the latest Token2 news, projects and events? Join our mailing list!